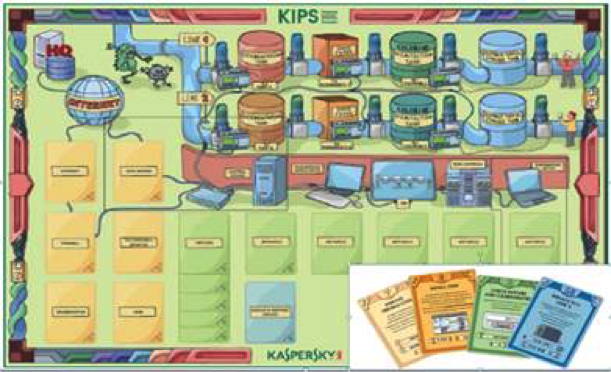
"Serious gaming" is the gamification of training for professional purposes. When you play a serious game, you are actually also improving your knowledge on a particular subject. For example, in 2015, the CERN Computer Security Team ran, in collaboration with an external security provider, the "Kaspersky Interactive Protection Simulation" (KIPS). Attended by about 80 control and safety system experts, technicians and engineers, the goal of the game was to instruct our control system experts how best to secure their installations. In the game, teams of four to six people had to secure a water purification plant round-by-round, by buying new security features and making sure that attackers did not bring the water treatment process to a halt. The team that generated the most revenue and had the least losses won (see details on this in our Bulletin article "Protect your Plant: A "Serious Game" about Control System Cyber-Security").
Nowadays, other online security games permit better in-depth training on a multitude of subjects. Take the CERN computer security course, for example, which you are supposed to complete to ensure you know the basics of computer security, password protection and CERN's rules. But there are more fancy ones:
- Google has produced an interesting quiz, challenging you to identify malicious e-mails;
- Radio Télévision Suisse's serious game aims to raise public awareness of the implications of data protection and Big Data;
- Less related to "computer security", but great for aspiring programmers: why not learn through playing how to develop code with JavaScript, Python and other languages.
Give these a try and enhance your skills in protecting your mailbox, your data and CERN!
________
Do you want to learn more about computer security incidents and issues at CERN? Follow our Monthly Report






