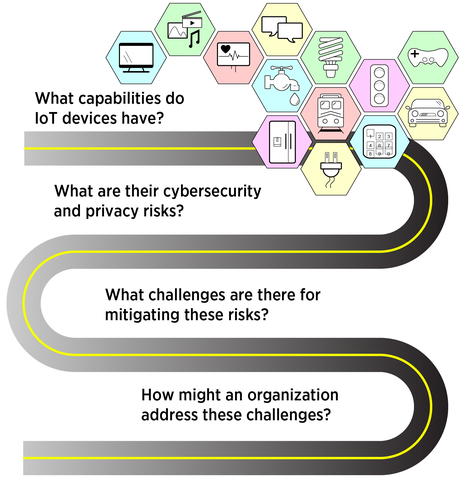
Seemingly every appliance we use comes in a version that can be connected to a computer network. But each gizmo we add brings another risk to our security and privacy. So before linking your office's new printer or coffee maker to the internet of things (IoT), have a look at an informational report from the National Institute of Standards and Technology (NIST) outlining these risks and some considerations for mitigating them.
Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks (NISTIR 8228) is the first in a planned series of documents NIST is developing to help IoT users protect themselves, their data and their networks from potential compromise. Developed by the NIST Cybersecurity for IoT Program over more than two years of workshop discussions and interaction with the public, NISTIR 8228 is primarily aimed at federal agencies and other big organizations that are incorporating IoT devices into their workplace - organizations that may already be thinking about cybersecurity on a large-scale, enterprise level.
"The report is mainly for any organization that is thinking about security on the level of the NIST Cybersecurity Framework," said Mike Fagan, a NIST computer scientist and one of the authors of the report. "It's targeted at the mode of thinking that an organization would have - more resources, more people, more ability, but also more risk of attack because of all those things. It's bad when a single house is attacked, but if a million bank account passwords are stolen, that has a much larger impact."
Larger organizations may already be using the Cybersecurity Framework and NIST SP 800-53 Rev. 5, two NIST resources that offer guidance for mitigating risk to information systems and the activities that involve them. NISTIR 8228 takes the security and privacy focus from these other documents and considers it in the context of IoT products, from thermostats to voice-operated devices, which may not have traditional interfaces such as a keyboard.
"An IoT device might even have no interface at all, or have no way to install security software," Fagan said. "But it still might connect to your network and be visible electronically to an enemy looking for a potential way in. It's this kind of incongruency with expectations that we want to help an organization think through before they bring IoT devices onto their network."
The report is a companion document to the Cybersecurity Framework and SP 800-53 Rev. 5. However, NISTIR 8228 offers only advice; none of its contents are requirements under the Federal Information Security Management Act (FISMA). After distinguishing IoT devices from conventional computers and outlining the type of risks they carry, the authors suggest three high-level risk mitigation goals:
- Protect device security, i.e., prevent an IoT device from being used to conduct attacks;
- Protect security of data, including personally identifiable information; and
- Protect individuals' privacy.
"IoT is still an emerging field," Fagan said. "Some challenges may vanish as the technology becomes more powerful. For now, our goal is awareness."
Specifics are around the corner, though. In the near future, NIST plans to release a core baseline document that aims to identify fundamental cybersecurity capabilities that IoT devices can include. The document will have all IoT devices in mind, including those for individual users and home networks.
"We plan to release a draft of the baseline document for public comment in July, and then we will hold a workshop on August 13 where we will gather feedback," Fagan said. "We'd like to help all IoT users be aware of the risks to their security and privacy and help them approach those risks with open eyes."