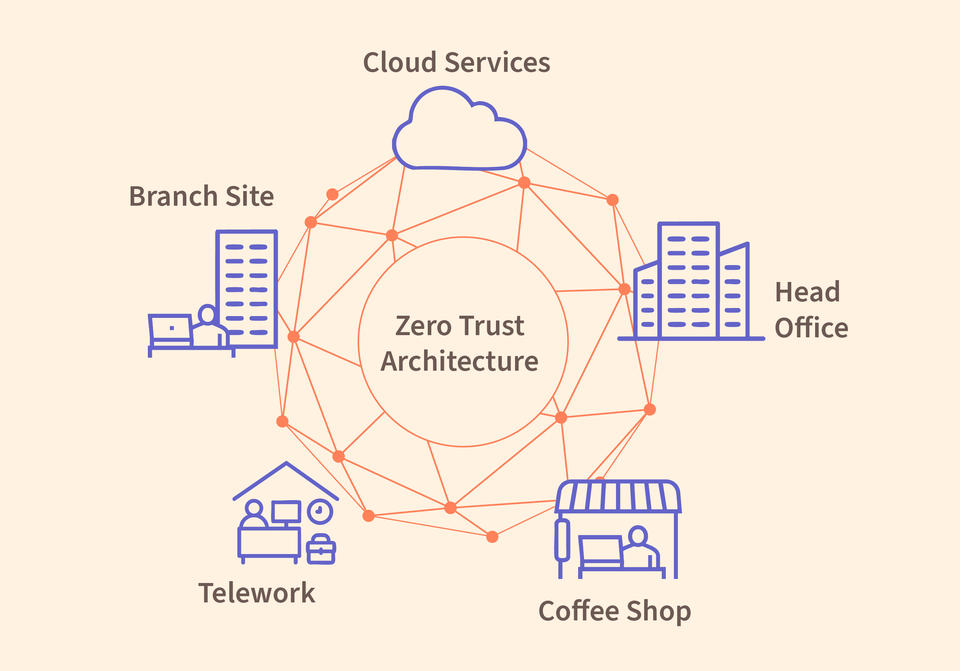
This is a complicated hybrid network with multiple vulnerabilities, and you can't just protect it with a simple firewall the way you would if all your assets were inside the Head Office. Zero trust architectures can help.
N. Hanacek/NIST
If you're trying to secure your organization's computer network from cyberattacks, traditional approaches may not work. Gone are the days when you could keep all your electronic assets inside a single building and construct a firewall between them and the wider internet. Now you have remote workers logging in from distant cities and cloud-based software applications running elsewhere in a data center. You've heard that your best bet for protecting all these far-flung assets is to create a zero trust architecture (ZTA), which assumes that no user or device can be trusted, regardless of its location or previous verification.
So how do you start?
Helping answer that question is the goal of newly finalized guidance from the National Institute of Standards and Technology (NIST). Implementing a Zero Trust Architecture (NIST Special Publication (SP) 1800-35) shows you how others have built ZTAs so that you can build your own. Developed through a project at the NIST National Cybersecurity Center of Excellence (NCCoE), the publication offers 19 example implementations of ZTAs built using commercial, off-the-shelf technologies. It also offers results and best practices from the 24 industry collaborators who participated in the project.
"Switching from traditional protection to zero trust requires a lot of changes. You have to understand who's accessing what resources and why," said Alper Kerman, a NIST computer scientist and co-author of the publication. "Also, everyone's network environments are different, so every ZTA is a custom build. It's not always easy to find ZTA experts who can get you there."
Older approaches to network security rely on the idea of a perimeter, where once a device gains entry it can then freely access the network's internal data, applications and other resources. This perimeter idea, developed when many networks were limited to a single location such as a building or campus, is growing obsolete. Nowadays a single organization may operate several internal networks, use cloud services, and allow for remote work - meaning there is no single perimeter.
This complexity has led to the development of the zero trust concept. ZTA implements a risk-based approach to cybersecurity - continuously evaluating and verifying conditions and requests to decide which access requests should be permitted, then ensuring that each access is properly safeguarded. Zero trust also prevents attackers who have gained access from roaming freely within the network and wreaking havoc as they go. Because of its effectiveness against both internal and external threats, ZTA adoption is increasing, and some organizations are required to use a ZTA.
"This guidance gives you examples of how to deploy ZTAs and emphasizes the different technologies you need to implement them," Kerman said. "It can be a foundational starting point for any organization constructing its own ZTA."
The new guidance augments NIST's 2020 publication Zero Trust Architecture (NIST SP 800-207), a high-level document that describes zero trust at the conceptual level. While the earlier publication discussed how to deploy a ZTA and offered models, the new publication gives users more help addressing their own needs, which can be a substantial task when implementing ZTA.
To assist the community, the NCCoE partnered with 24 industry collaborators including several major tech companies. The NCCoE team and its collaborators spent four years installing, configuring and troubleshooting the example implementations, as well as working together closely on the details in the publication. While the guidance mentions the use of commercially available technologies, their inclusion does not imply recommendation or endorsement by NIST or NCCoE.
"This guidance gives you examples of how to deploy ZTAs and emphasizes the different technologies you need to implement them. It can be a foundational starting point for any organization constructing its own ZTA." -Alper Kerman, NIST computer scientist
The team built the new guidance around real-world situations that large organizations typically confront. It details the implementation and test results for a number of use cases and scenarios that simulate the complexity of modern enterprise networks, such as one with multiple cloud platforms, a branch office and a simulated coffee shop offering public WiFi access for remote employees.
Kerman describes the publication as a comprehensive document that details the problem and solutions to it, along with the scenarios the project team tested and the technologies they used. It also references how the documented solutions map to various cybersecurity frameworks, chiefly those in the NIST Cybersecurity Framework and NIST SP 800-53.
As with all other NCCoE projects, Kerman said, this one has the goal of illustrating solutions to a cybersecurity challenge using commercial technology.
"The examples the guidance provides are demonstrations," he said. "They can help organizations understand some of the capabilities they have to have on board to deploy a ZTA."






